Few partnerships have been as impactful as the one between NowSecure and the OWASP Mobile App Security (MAS) project. Today, as we celebrate three years of NowSecure as an OWASP MAS Advocate, we reflect on a journey marked by innovation, collaboration, and continuous improvement that has set the blueprint for future industry partnerships.

Being a MAS Advocate means making high-impact contributions. NowSecure has delivered consistently, offering dedicated time from key experts, especially project leader Carlos Holguera, and stepping in with additional support whenever needed.
GitHub tells a compelling story about NowSecure's involvement in the OWASP MAS project over the past three years:
- 320+ Pull Requests
- 230+ Reviews
- 42,000+ Additions
- 29,500+ Deletions
These numbers reflect more than just activity, they demonstrate leadership. NowSecure has significantly enhanced OWASP MAS resources by contributing valuable content, reviewing community submissions, and maintaining the overall clarity and quality of the project.
But there's more to it than just numbers. NowSecure has been a driving force behind the evolution of the OWASP MAS project, providing strategic insights, technical expertise, and a commitment to excellence that has shaped our direction and impact. Below, we look back on the key milestones and contributions over the past few years, a timeline that highlights the valuable role NowSecure has played in each step of the evolution of the MAS project.
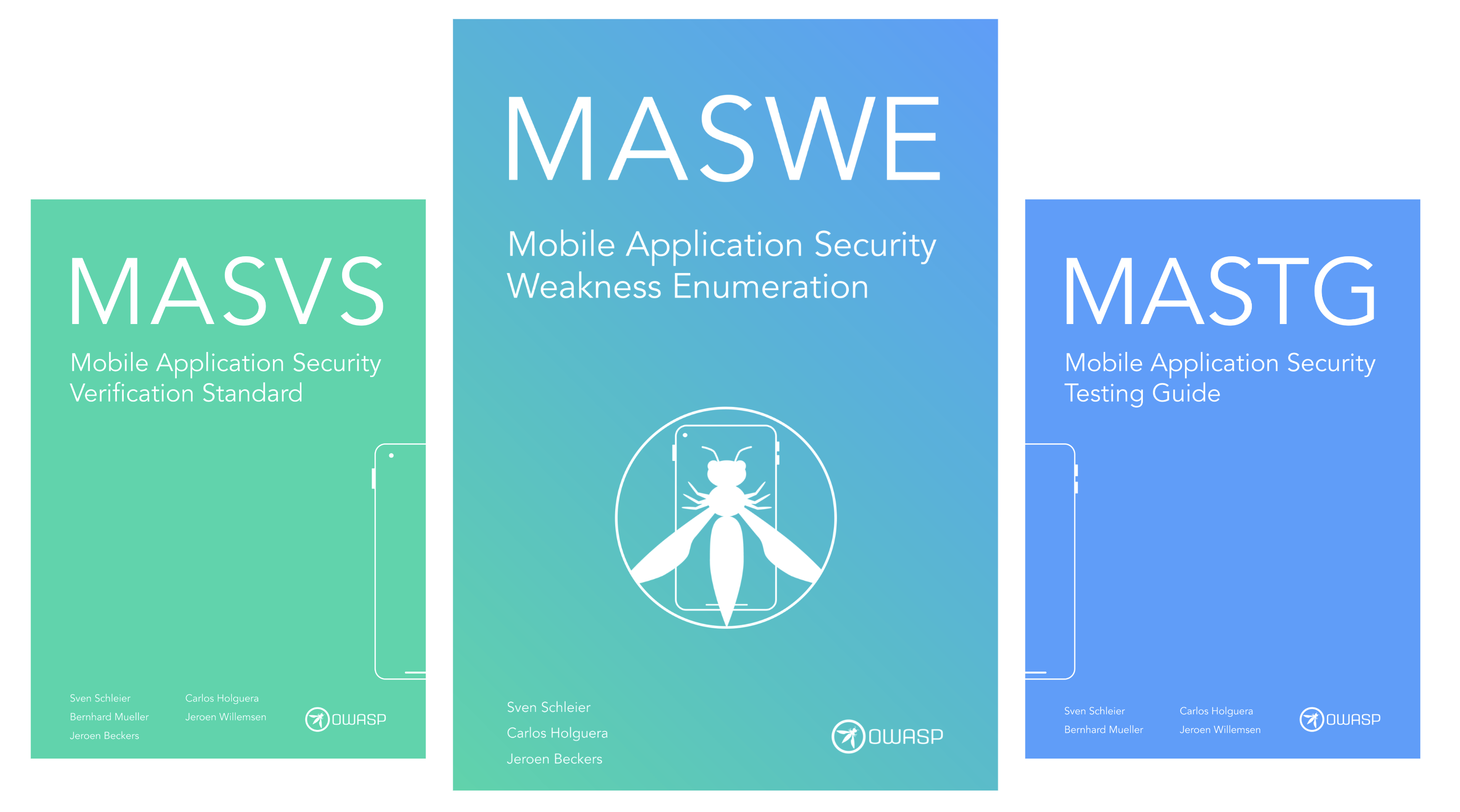
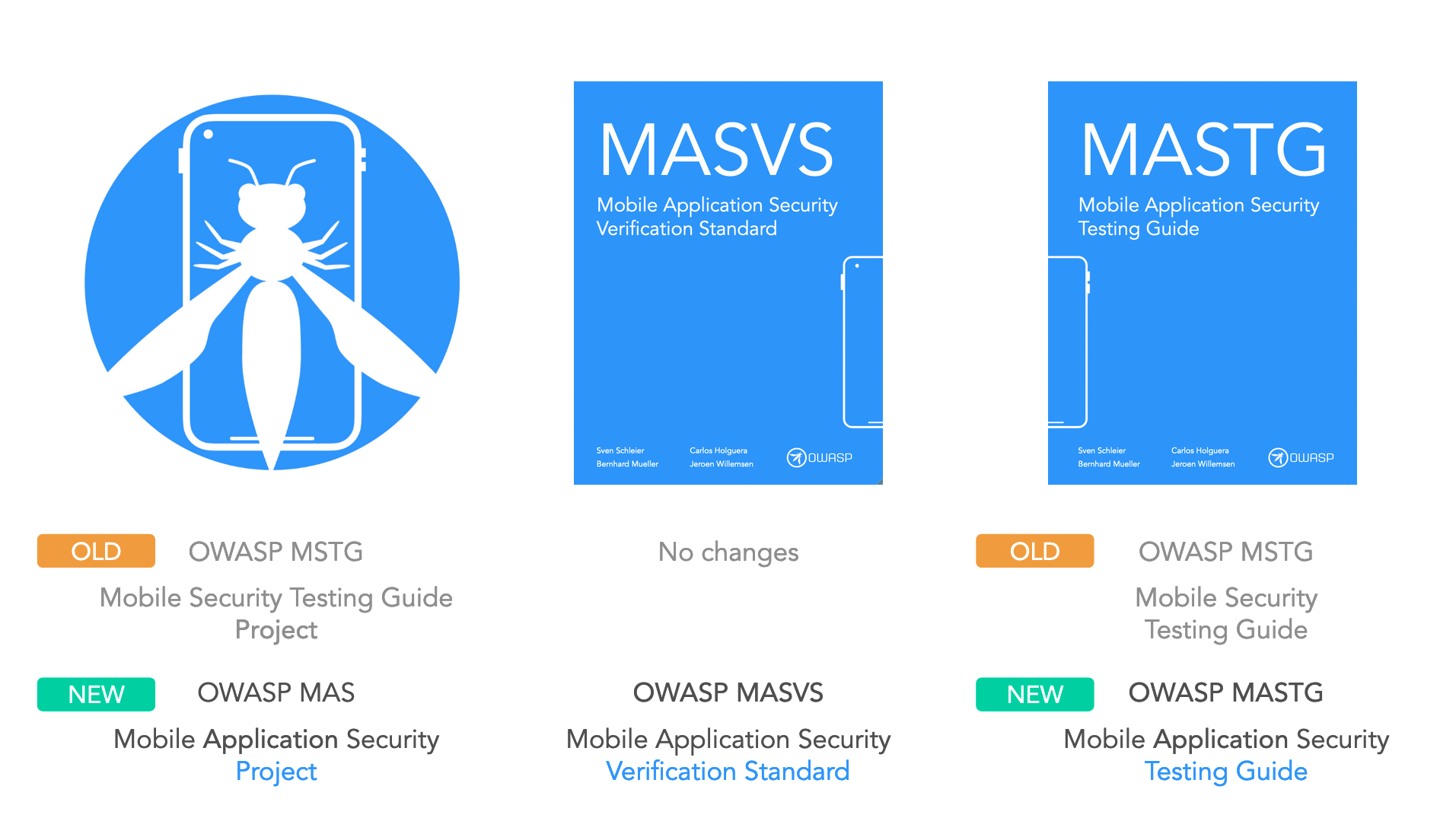
In August 2022, we announced a rebranding of the project, formerly known as the "OWASP Mobile Security Testing Guide (MSTG)" project. The new identity, OWASP Mobile App Security (MAS), better reflects the full scope of our project, from the MAS Verification Standard (MASVS) and MAS Testing Guide (MASTG) to checklists and crackmes. And later, the Mobile App Security Weakness Enumeration (MASWE).
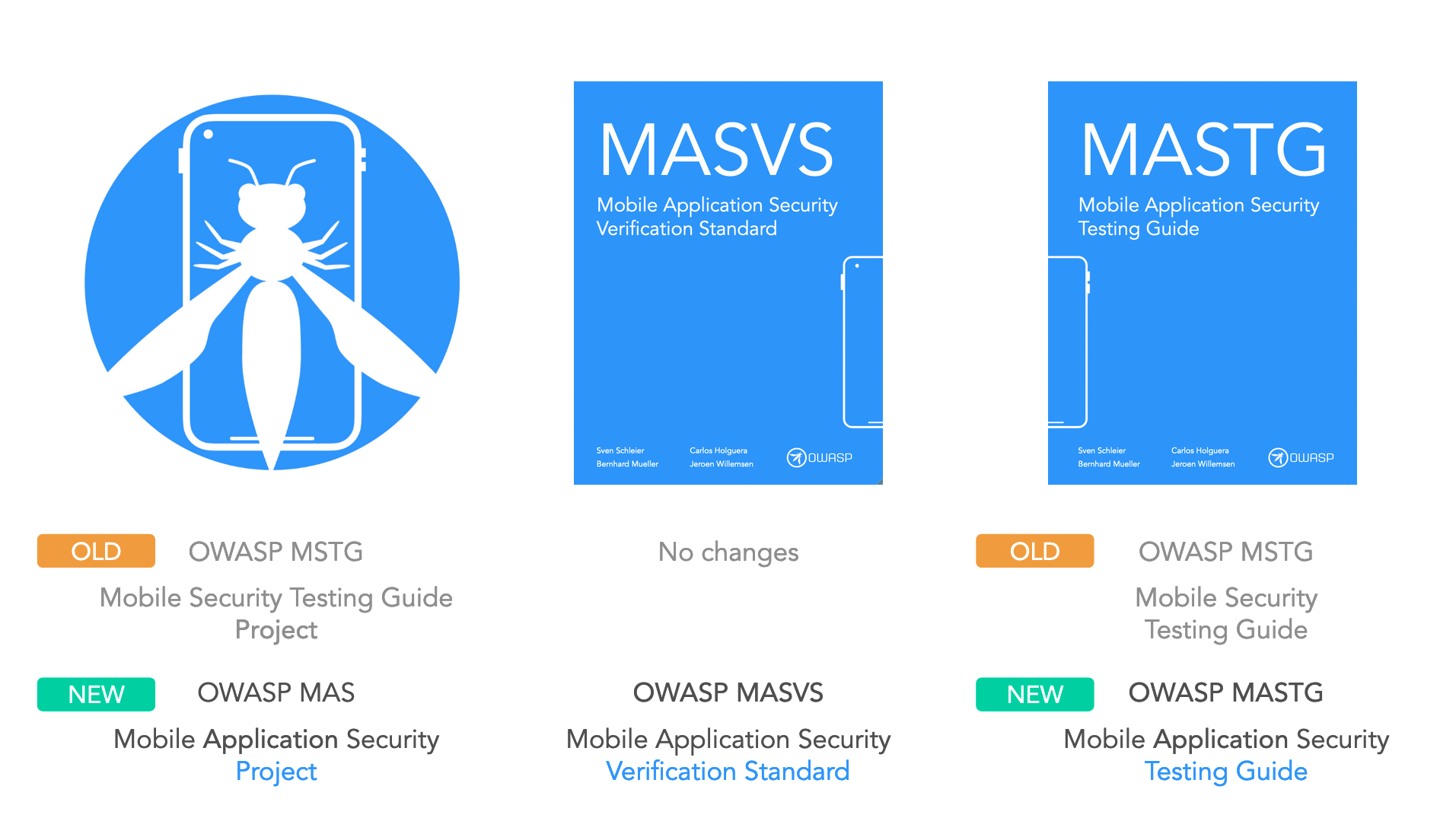
NowSecure provided strategic insight and industry perspective that helped clarify the project's scope and messaging. Their early feedback ensured that the new brand not only resonated with the community but also set a clear direction for future enhancements.
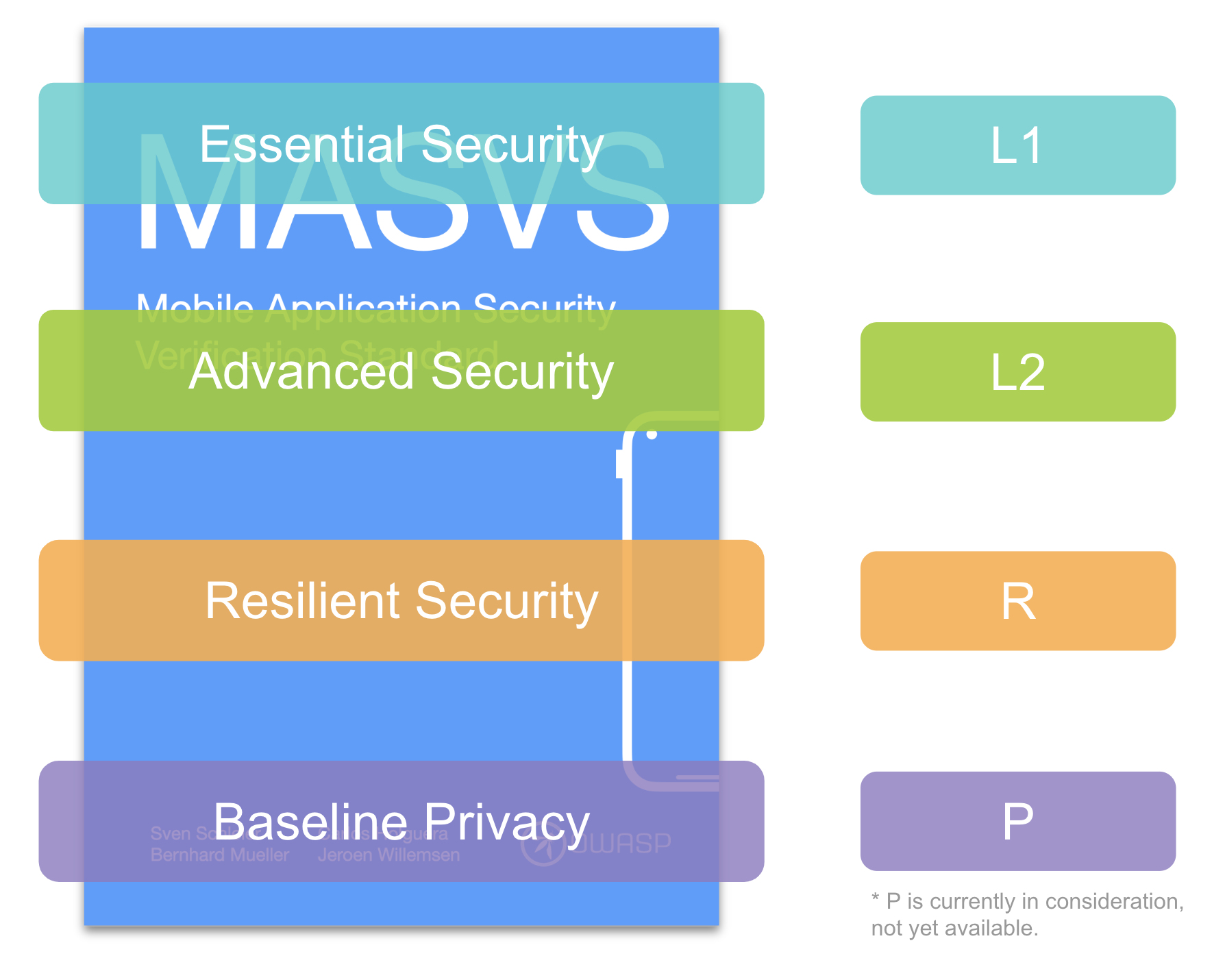
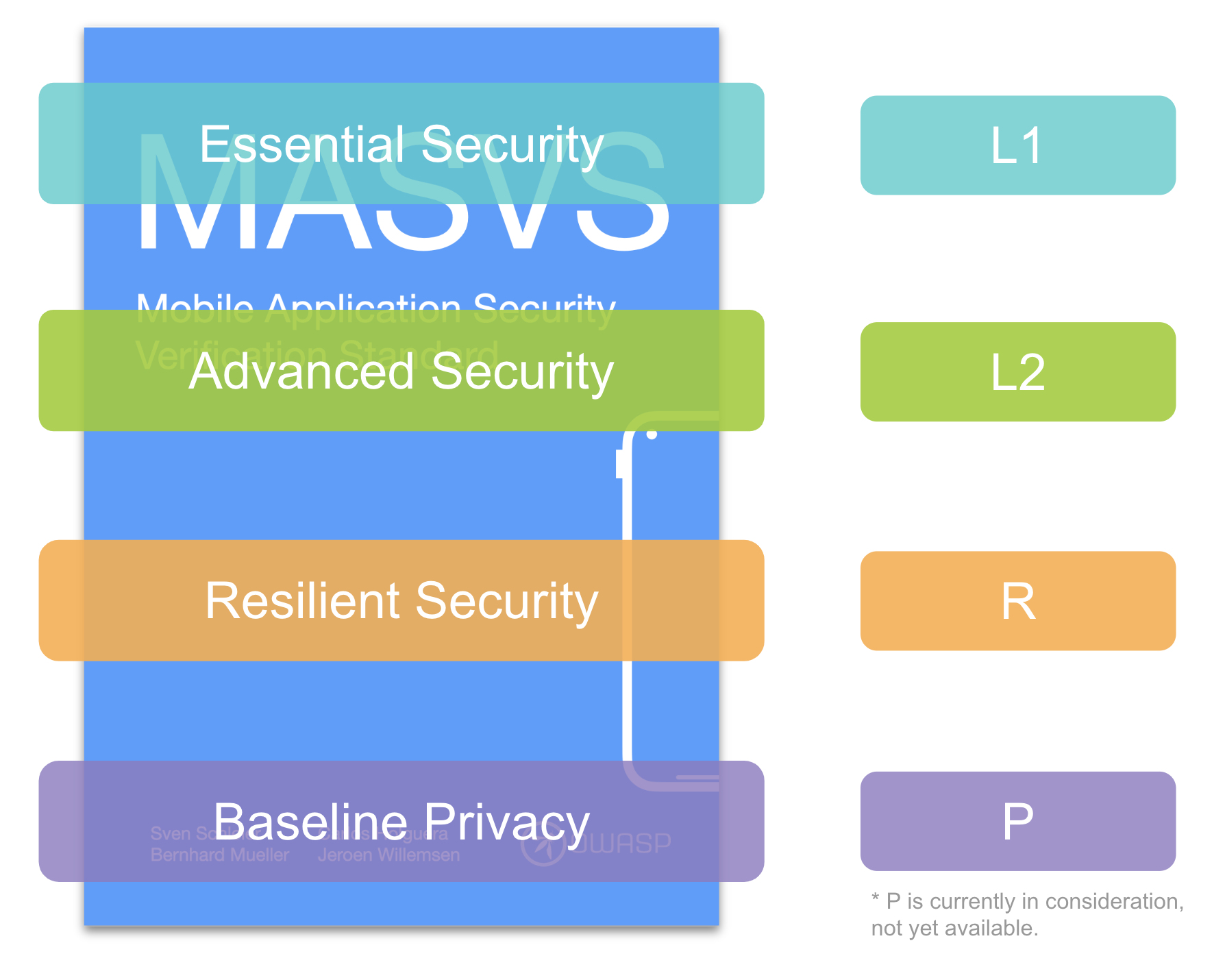
April 2023 saw the launch of MASVS v2.0.0, a major milestone that redefined mobile app security standards. This release introduced crucial improvements:
- Abstraction & Simplification: Redundant controls were removed, making MASVS more approachable for developers.
- Clarity Through Standardization: Leveraging and referencing well-established standards ensured that our controls were clear and actionable.
- Introduction of MAS Testing Profiles: Transitioning from the previous "levels" to new "profiles" allowed for more tailored assessments in real-world scenarios.

NowSecure's technical expertise and continuous feedback during the development process were instrumental. Their real-world testing scenarios and rigorous review of the proposed changes helped shape a standard that truly meets the needs of modern mobile app security professionals.
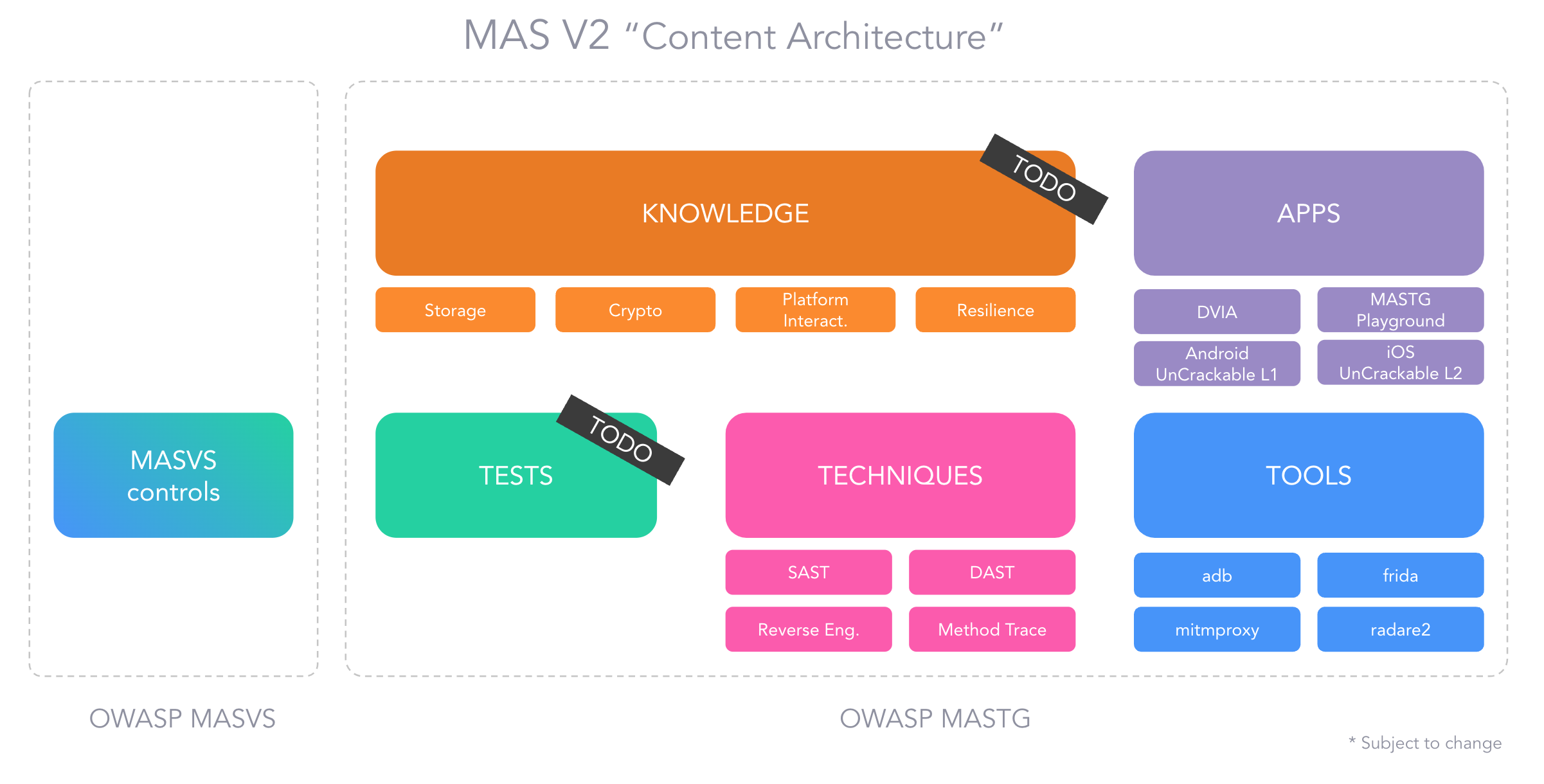
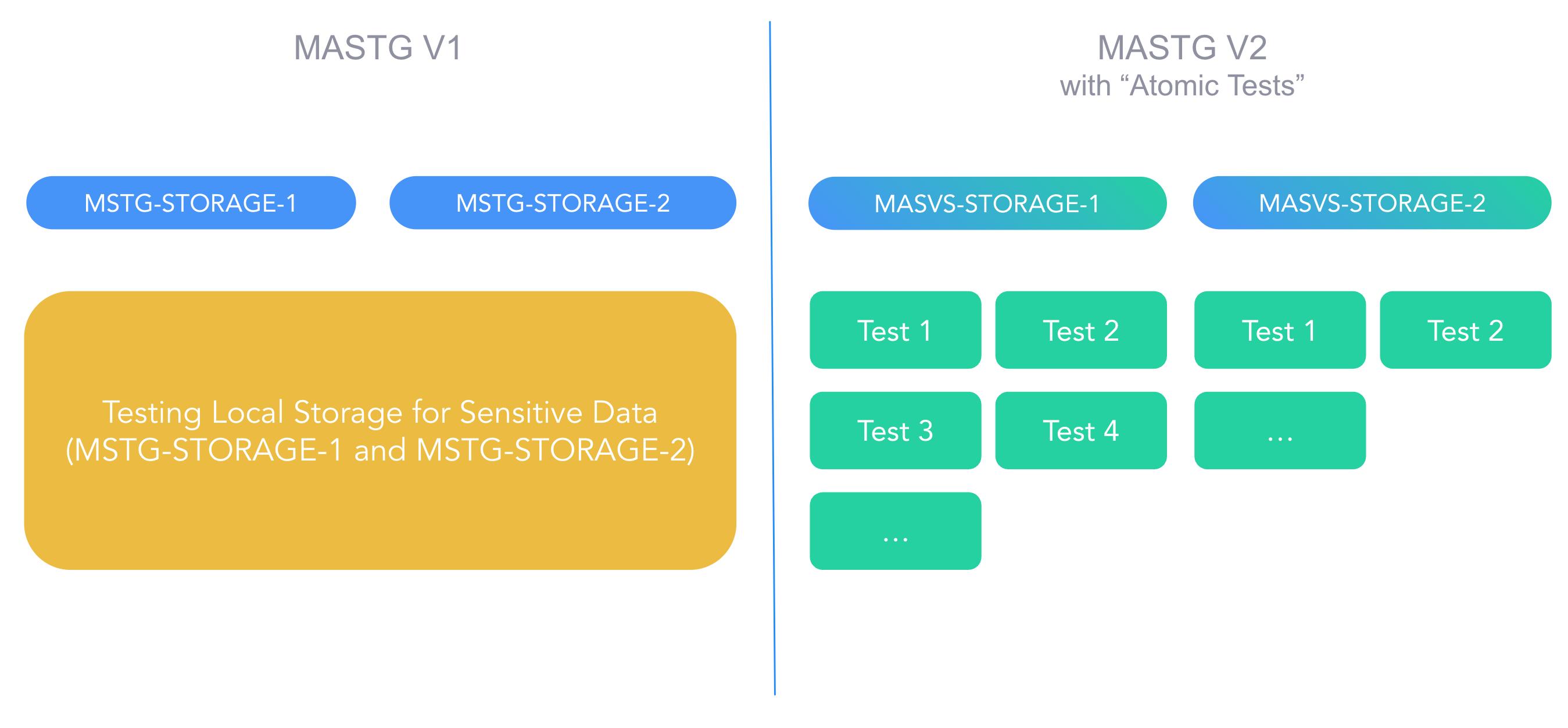
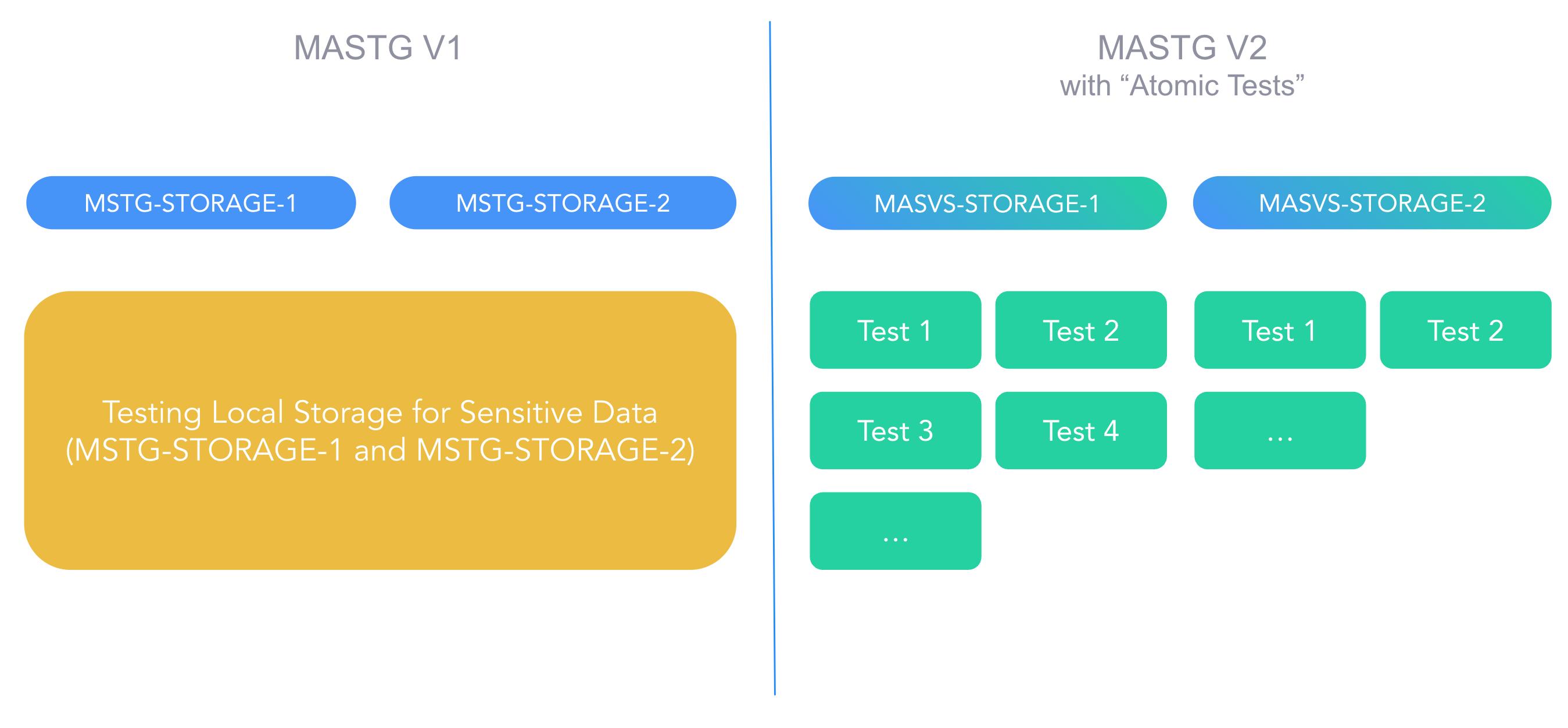
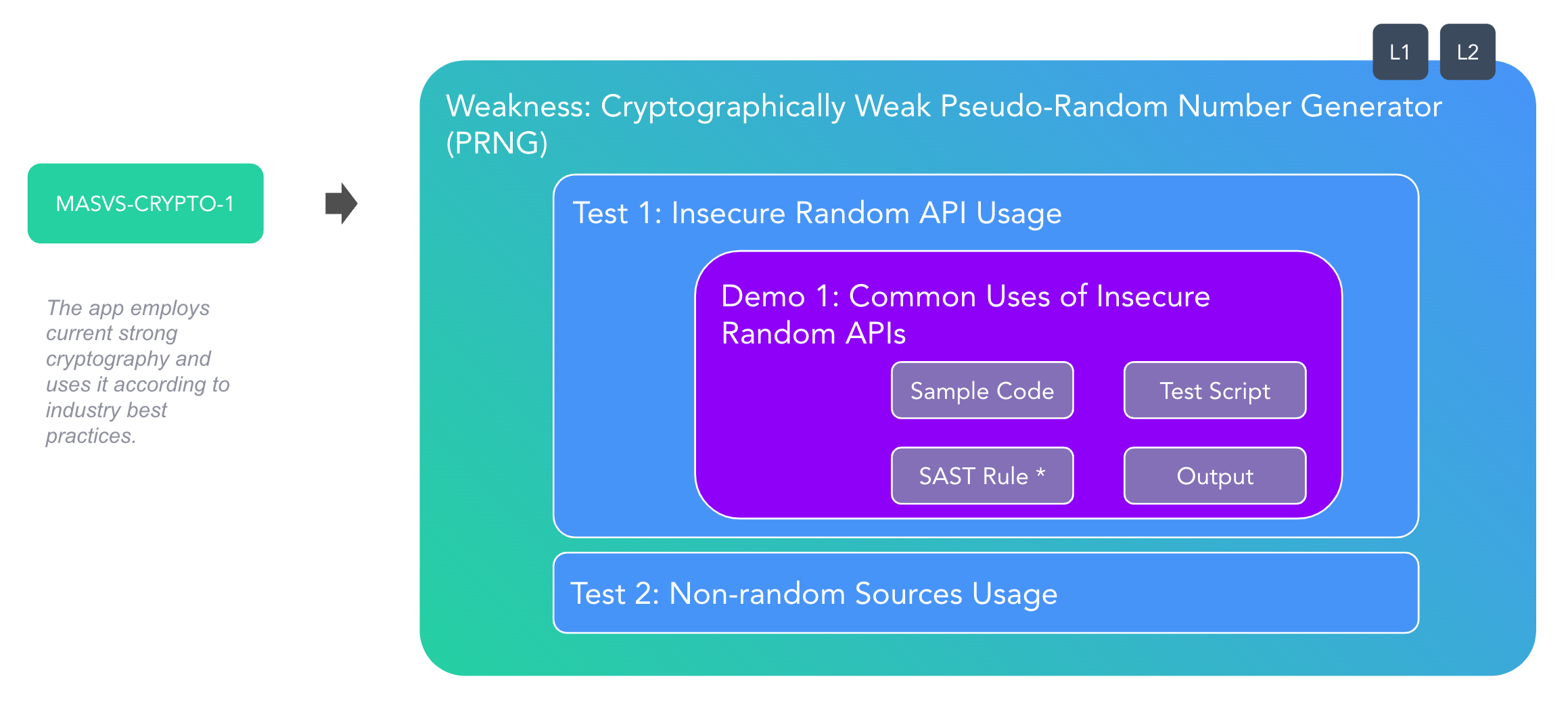
In July 2023, we announced the first phase of the MASTG refactor, including:
- New MAS Testing Profiles: Replacing traditional verification levels with "profiles" backed-up by real-world scenarios. This change allows for more tailored assessments, making it easier to understand the context and applicability of each test.
- Atomic Tests: Breaking down large tests into smaller, self-contained units has reduced ambiguity and improved traceability.
Throughout this process, NowSecure's in-depth technical reviews and pilot testing were invaluable. Their willingness to experiment with early versions of the refactored tests ensured that the new structure was both robust and practical for real-world application, ultimately enhancing the overall quality and consistency of the MASTG.
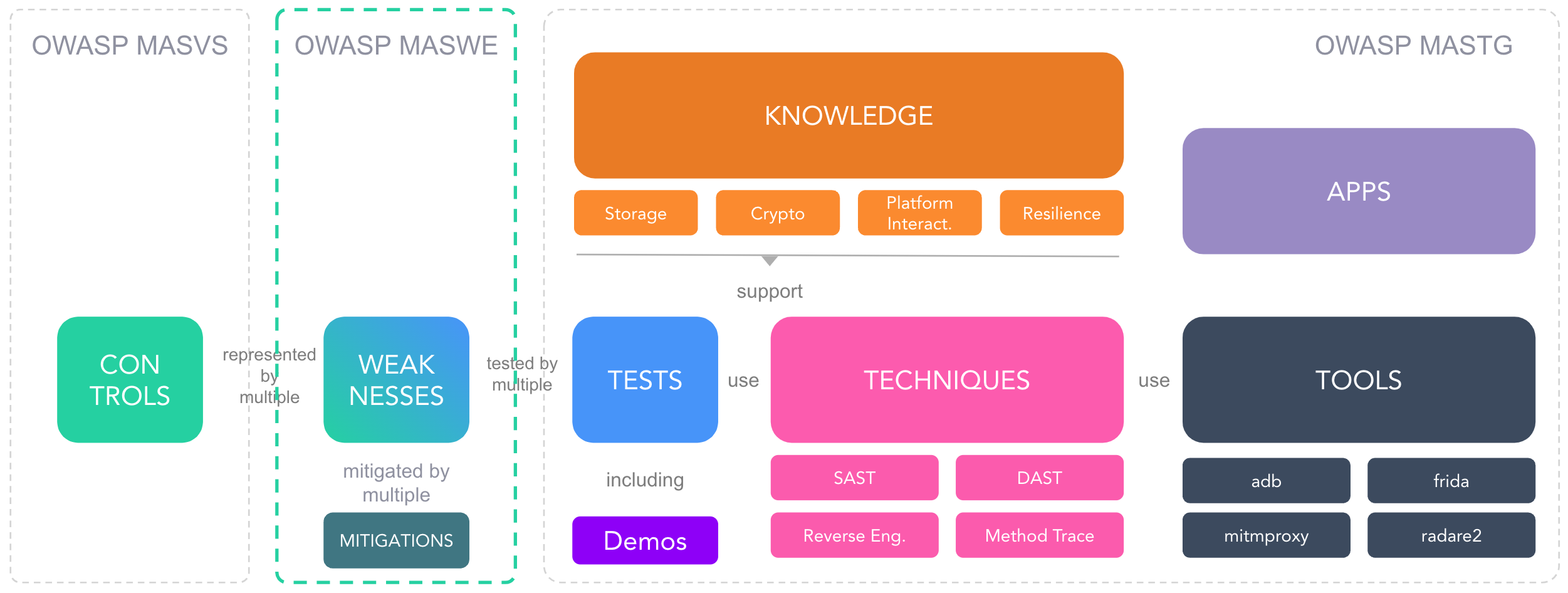
Later in September 2023, we announced the second phase of the MASTG refactor, focusing on a modular approach:
- The guide was reorganized into distinct components—Tests, Techniques, Tools, and Apps—making it easier to locate and reference specific content.
- This modularity enhances cross-referencing and maintainability of the overall framework.
NowSecure provided critical feedback on the modularization process and performed the implementation of the new structure. Their insights into how security professionals interact with the MASTG helped shape a more user-friendly and efficient resource.
October 2023 marked a significant expansion in our scope with the introduction of MASVS-PRIVACY as a proposal which was later included into the release of MASVS v2.1.0 in January 2024 after community and industry-wide thorough review.

NowSecure's leadership in mobile security and privacy issues was a driving force behind this addition. Their proactive stance on privacy concerns and hands-on experience with data protection challenges contributed to shaping a robust baseline that addresses modern privacy demands.
In February 2024, we launched the MAS Task Force, a focused group of mobile security experts who meet monthly to drive the MAS project roadmap forward. Their efforts include managing GitHub issues, refining new MAS profiles and risks, assigning tasks, and developing vulnerable code snippets for both Android and iOS. Currently, the group is focused on porting V1 tests to V2 in preparation for MASTG V2.

NowSecure's continued support plays a key role in making this initiative possible. By enabling Carlos Holguera to dedicate time and expertise to lead the effort, the task force has maintained strong momentum. With a combination of technical depth and strategic direction, Carlos has helped the group prioritize effectively and push the MAS project forward with consistency and clarity.
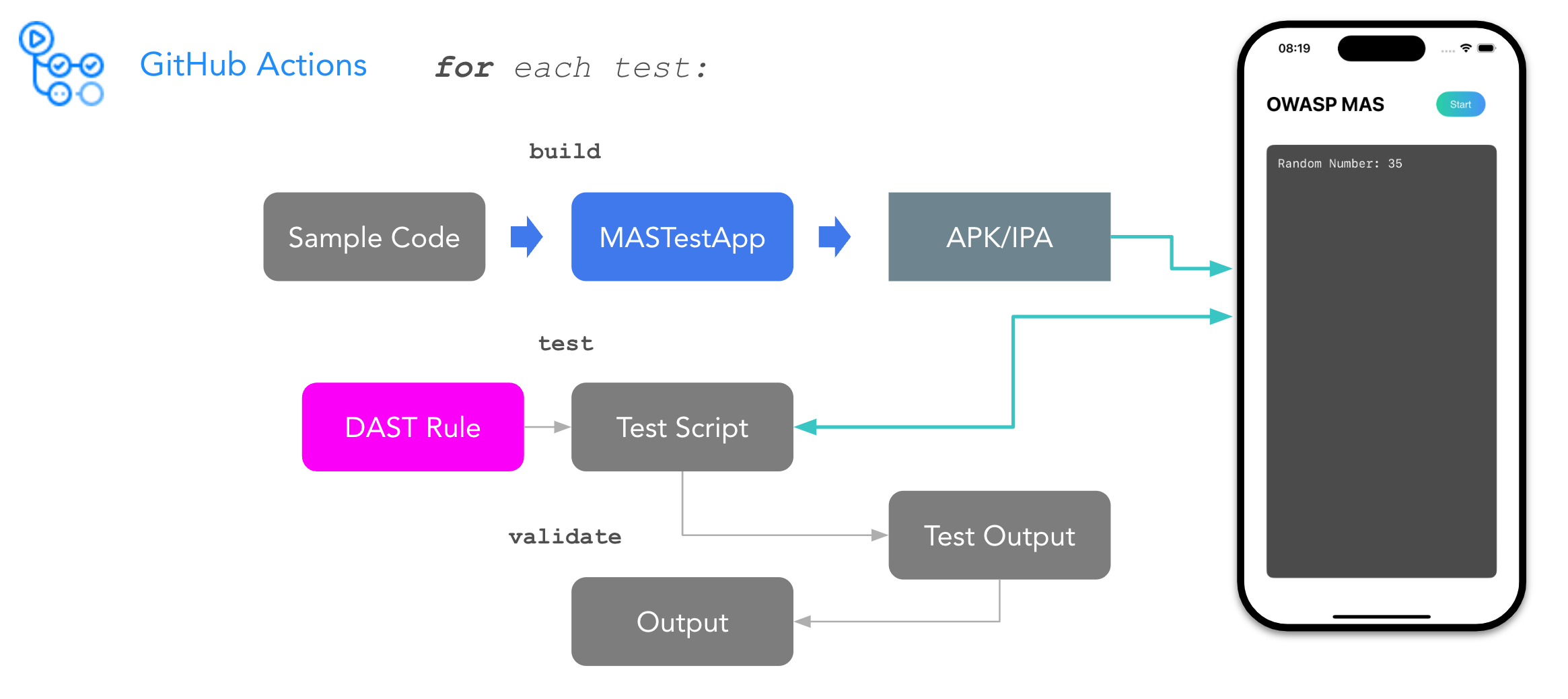
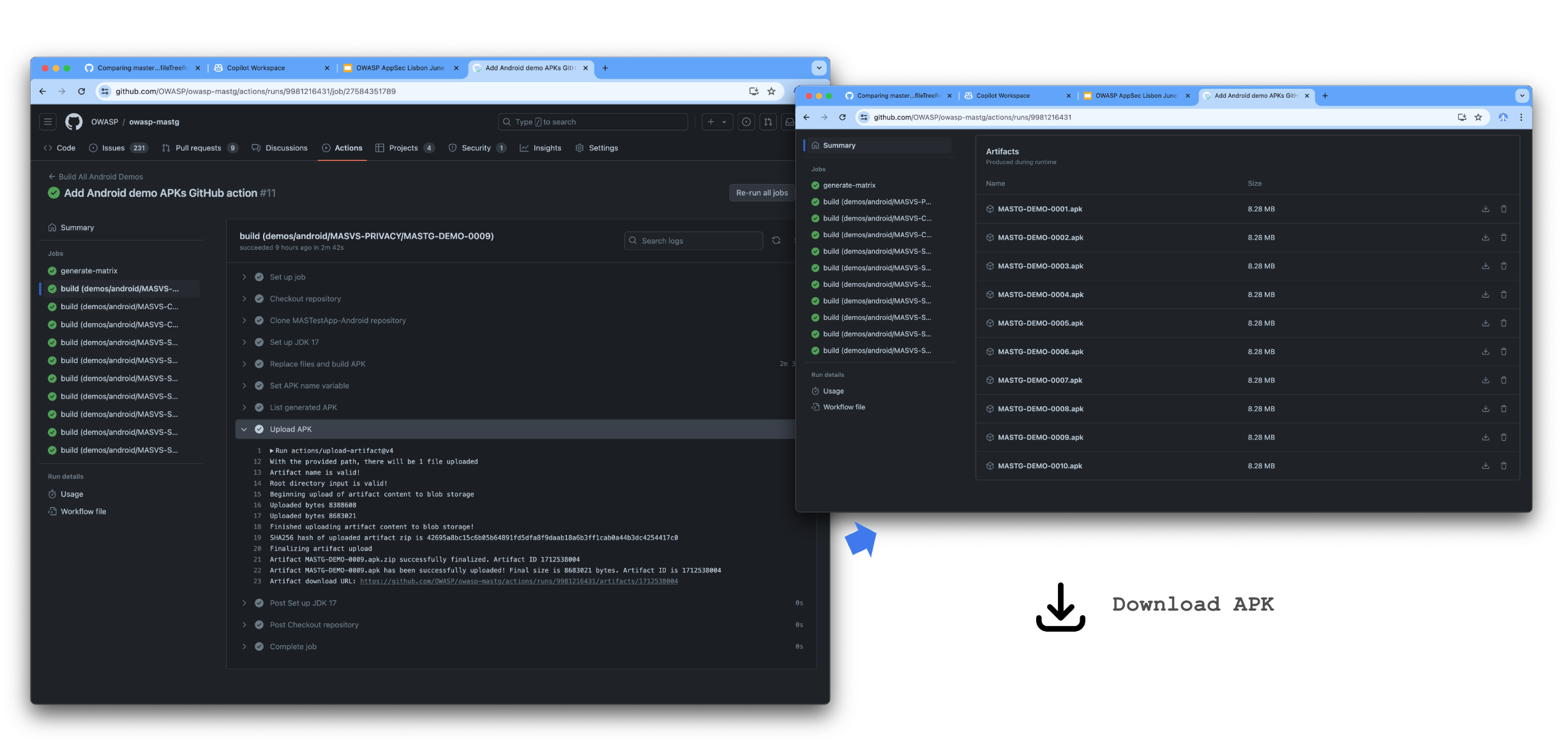
In May 2024, we launched new MAS Test Apps for Android and iOS, designed to facilitate hands-on learning and testing. These apps include:
- Skeleton Applications: Basic frameworks for Android and iOS, allowing users to explore and validate security scenarios.
- Code Samples: Embedded within the apps, these samples demonstrate best (and worst) practices and common pitfalls in mobile app security.
- Build Automation: Leveraging GitHub Actions, we automated the build and MASTG integration process for these demos, ensuring that they remain up-to-date and functional.
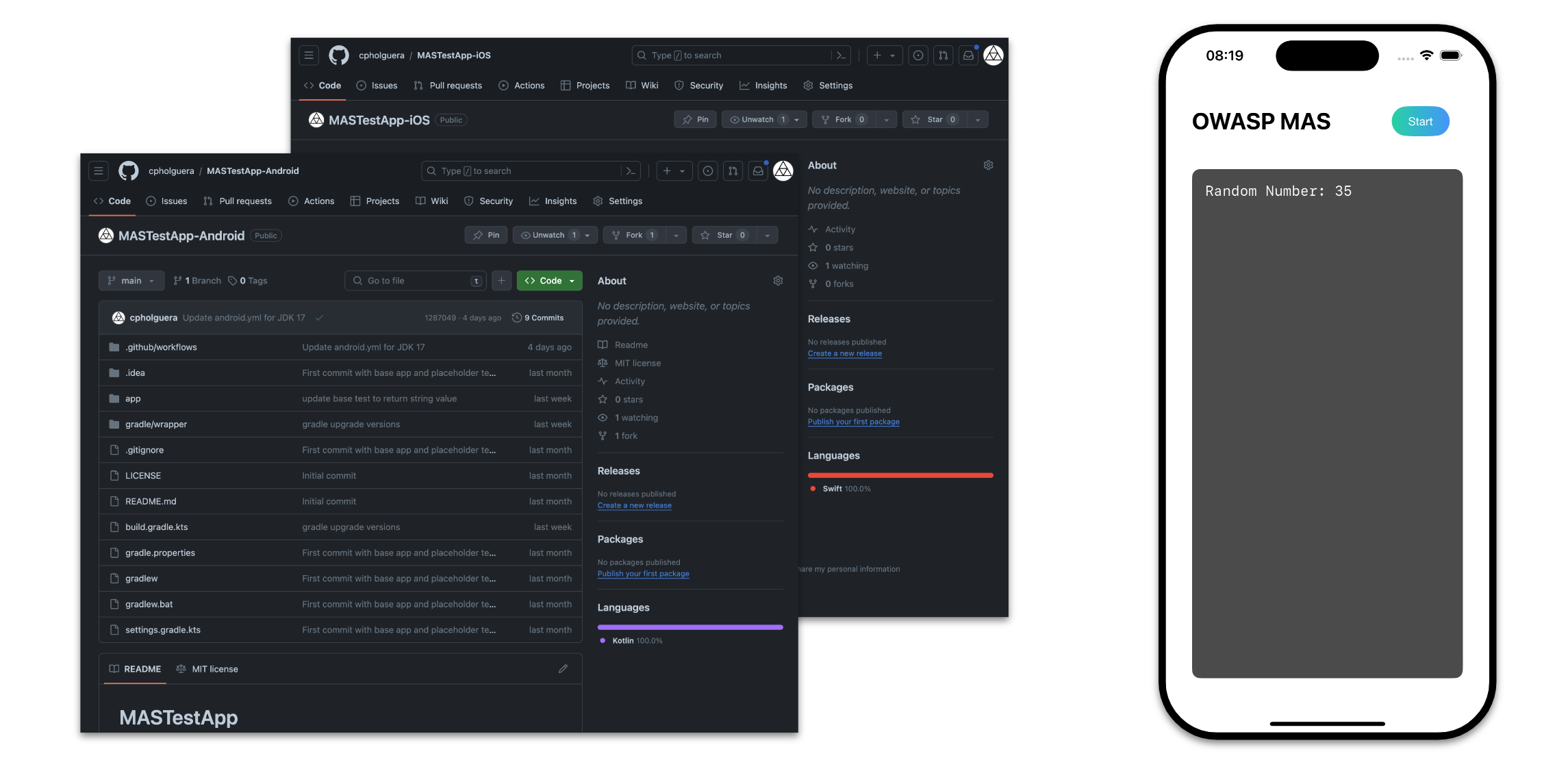
NowSecure's expertise in mobile app security testing was invaluable in the development of these test apps. Their insights into real-world vulnerabilities and hands-on experience with mobile security challenges helped shape the design and functionality of the apps, ensuring that they are both practical and effective for users.
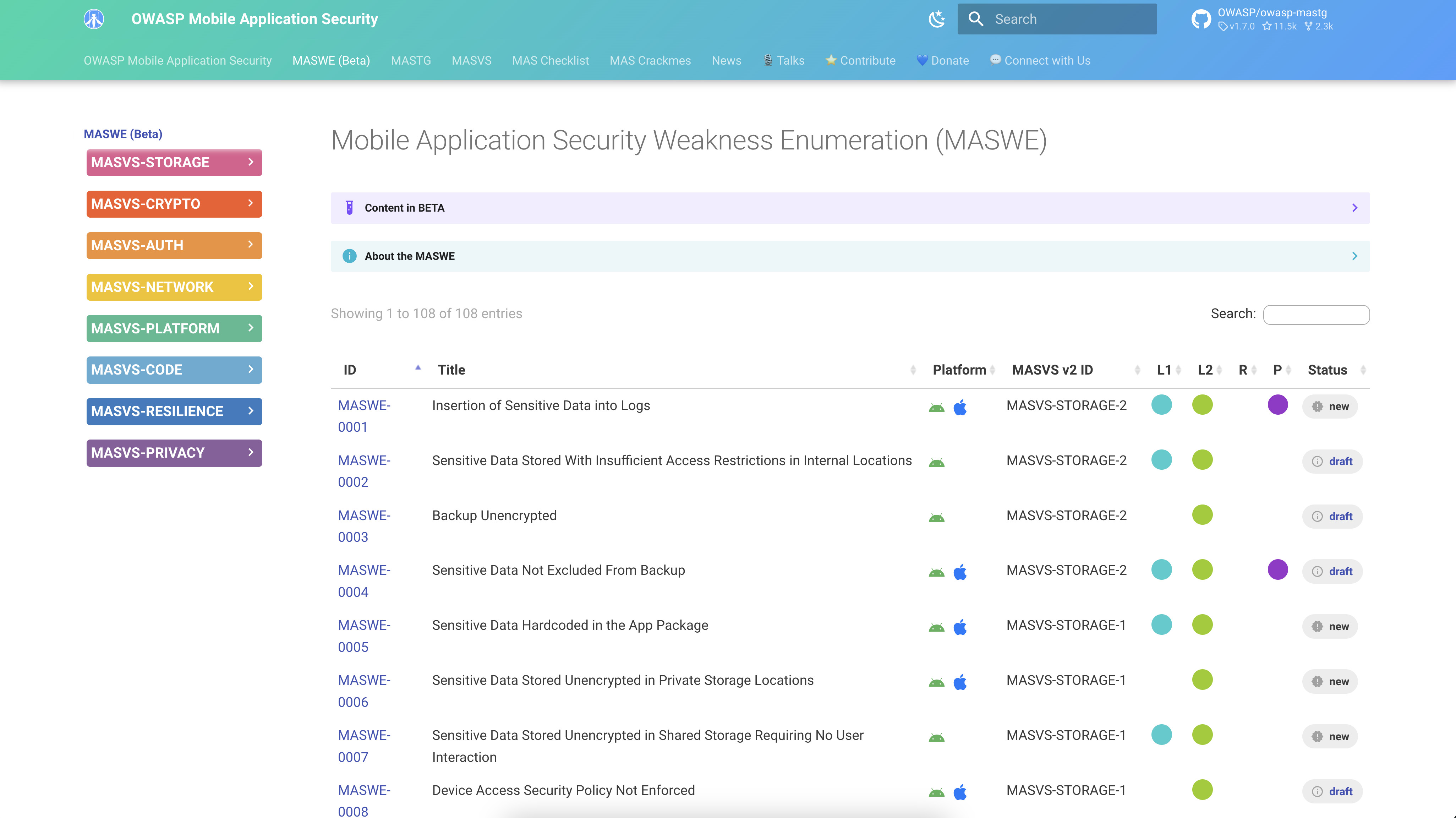
July 2024 saw the introduction of the Mobile App Security Weakness Enumeration (MASWE):
- MASWE bridges the gap between high-level MASVS controls and detailed MASTG tests.
- It offers a granular view of specific weaknesses, enhancing traceability from requirements down to individual test cases.
NowSecure's comprehensive review and detailed feedback on early drafts of MASWE were critical. Their ability to pinpoint real-world vulnerabilities and suggest actionable improvements helped shape MASWE into a tool that complements both MASVS and MASTG, ensuring that our framework remains holistic and responsive to emerging threats.
In November 2024, we hosted the OWASP Project Summit, where NowSecure led the mobile app security track. This five-day event brought together experts from various companies to discuss the future of mobile security, share insights, and collaborate on innovative solutions. During the summit, approximately 40 pull requests were created, and countless discussions were held.

NowSecure played a key role by reviewing the contributions and driving technical discussions, ensuring that the ideas generated were actionable and aligned with the project's goals. Under the leadership of Carlos Holguera, who helped organize and guide the track, NowSecure fostered an environment of collaboration and knowledge sharing—setting a high standard for future OWASP events.
As we celebrate this three-year partnership, we're excited about what lies ahead. These contributions aren't just milestones, they're building blocks for the future. Thanks to the incredible community support, ongoing advocacy, and passion of organizations like NowSecure, the next chapters of the MAS project promise even greater innovation and impact in the years to come.
We invite you to join us on this journey, share your insights, and contribute to shaping the future of mobile security.
Thank you, NowSecure, for being a beacon of excellence and a trusted partner in our mission to secure mobile applications worldwide.








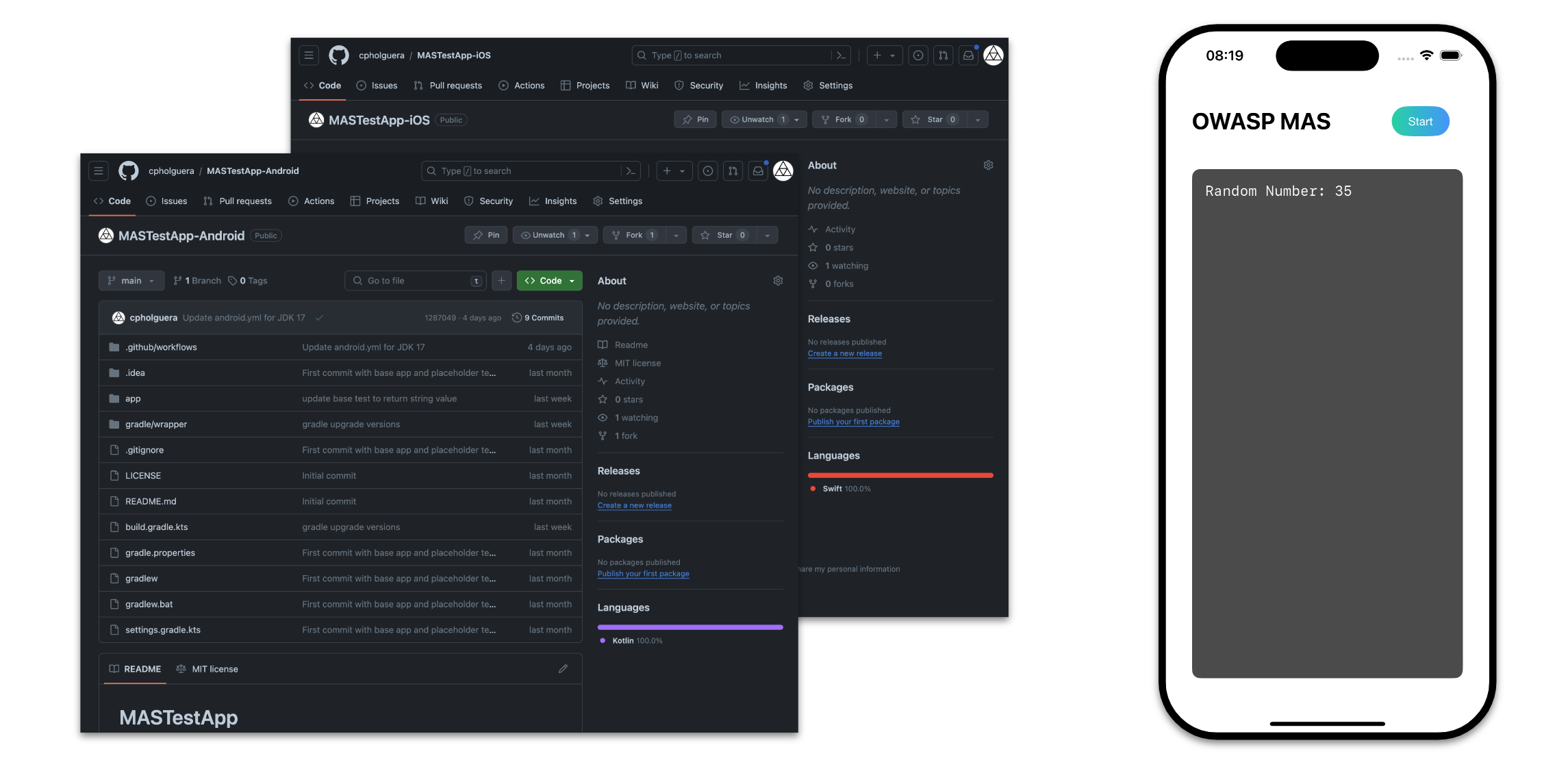

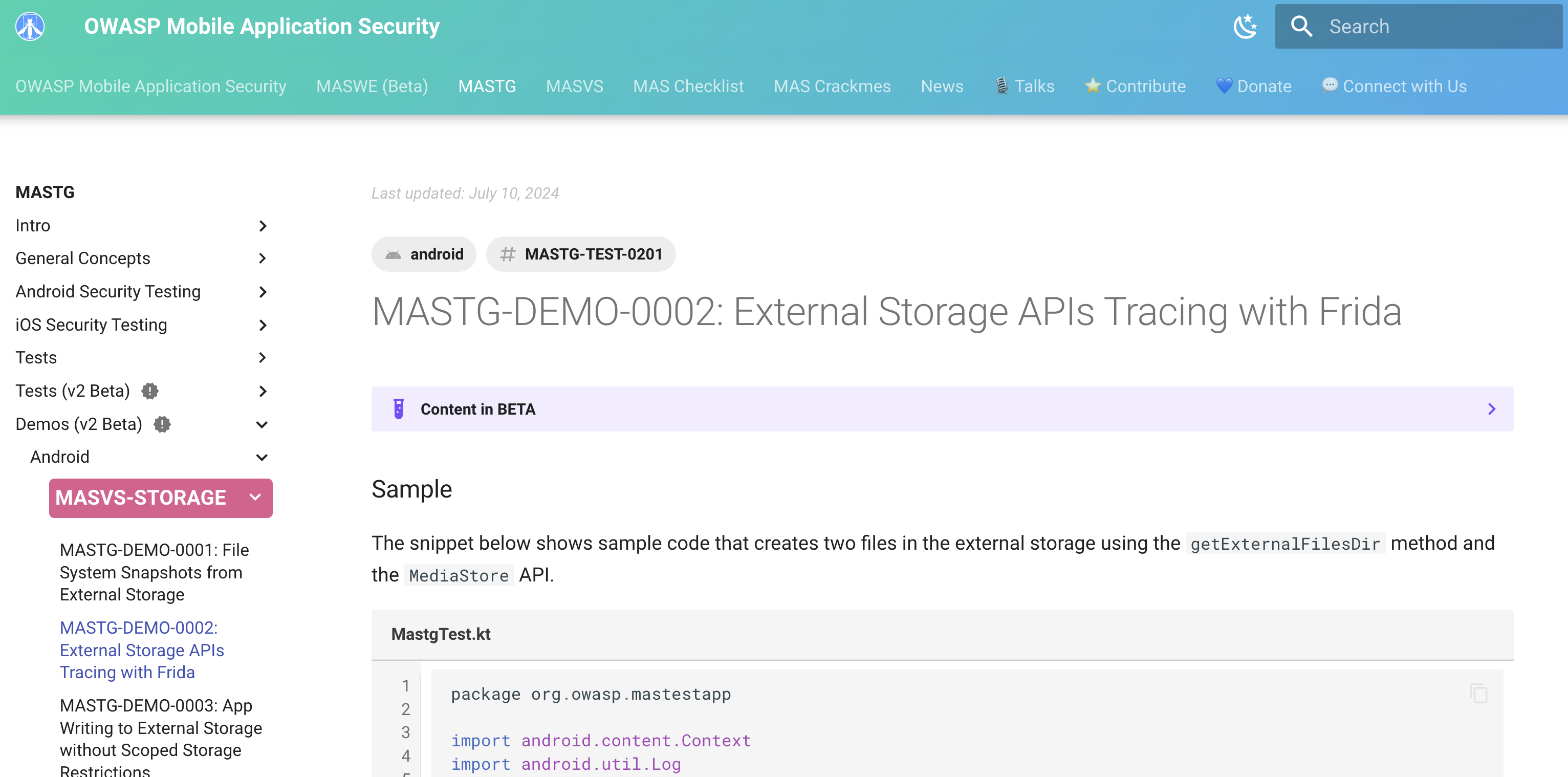
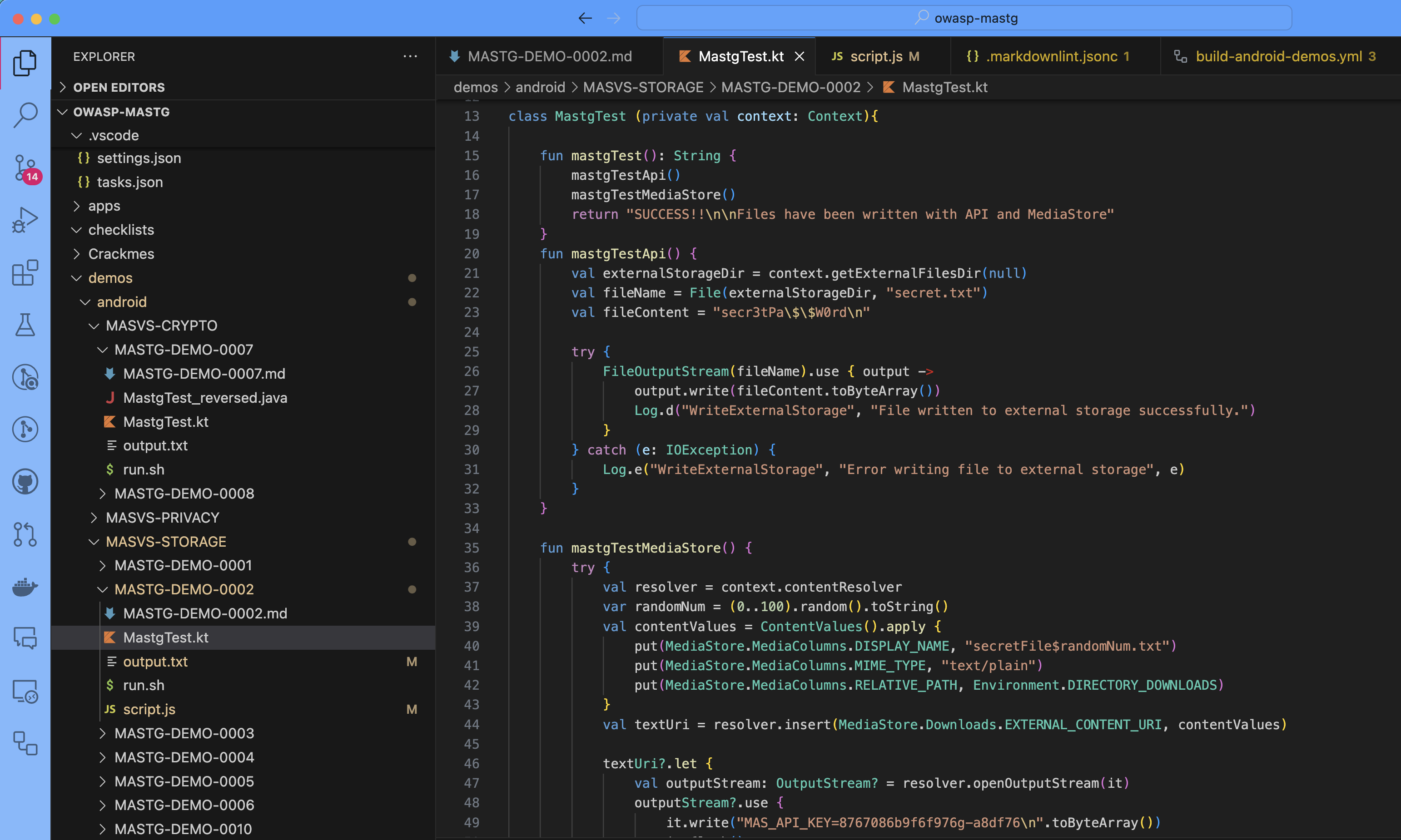
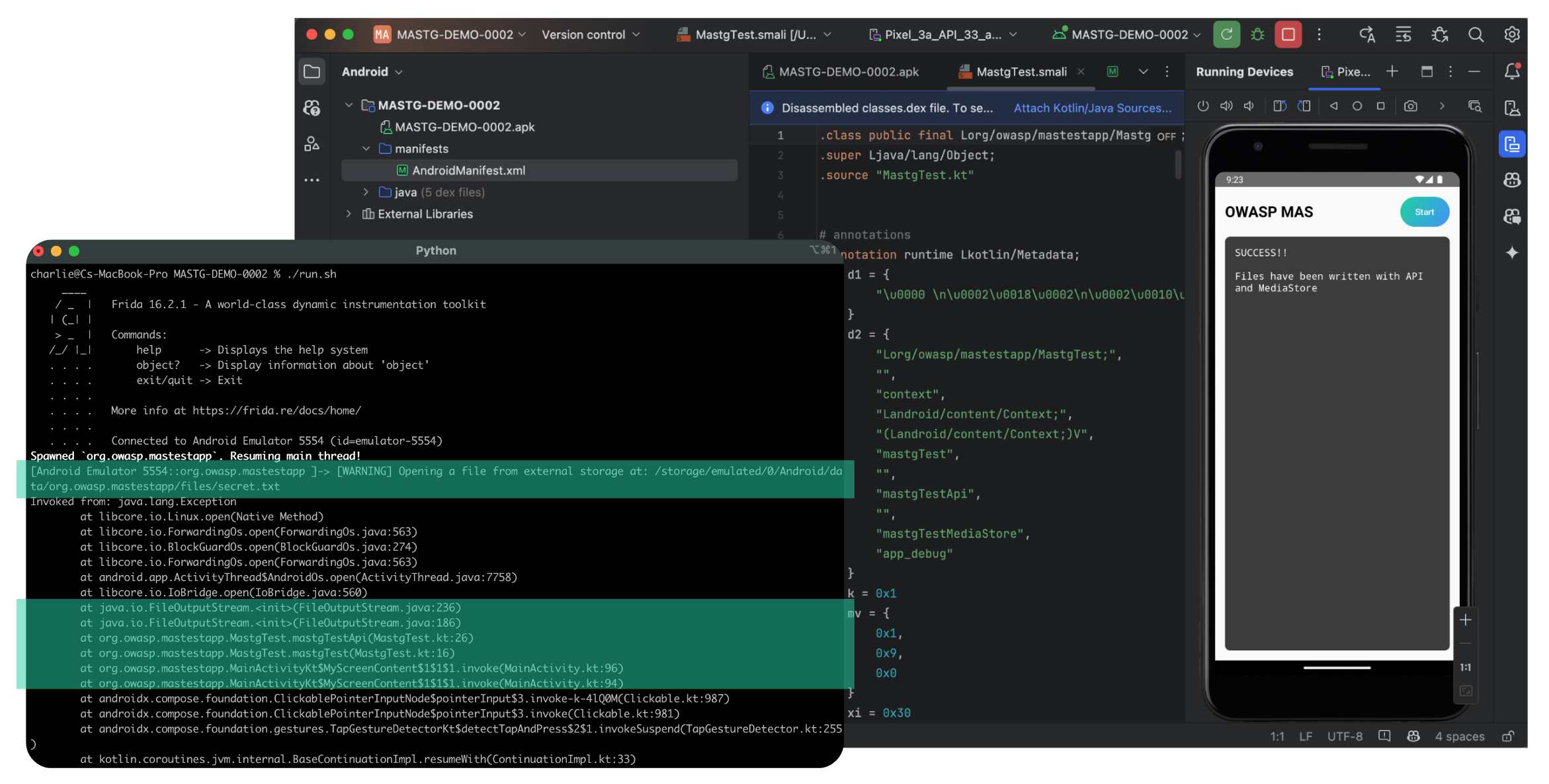
 These demos can also be used as experimental playgrounds to improve your skills and practice with different cases as you study mobile app security with the MASTG. For example, you can try to reverse engineer the app and see if you're able to find the same issues as the demo or you can try to fix the issues and see if you can validate the fix.
These demos can also be used as experimental playgrounds to improve your skills and practice with different cases as you study mobile app security with the MASTG. For example, you can try to reverse engineer the app and see if you're able to find the same issues as the demo or you can try to fix the issues and see if you can validate the fix.