MASTG-TECH-0095: Method Hooking
Frida¶
In Execution Tracing, we used frida-trace when navigating to a website in Safari and found that the initWithURL: method is called to initialize a new URL request object. We can look up the declaration of this method on the Apple Developer Website:
- (instancetype)initWithURL:(NSURL *)url;
Using this information, we can write a Frida script that intercepts the initWithURL: method and prints the URL passed to it. The full script is below. Make sure you read the code and inline comments to understand what's going on.
import sys
import frida
# JavaScript to be injected
frida_code = """
// Obtain a reference to the initWithURL: method of the NSURLRequest class
var URL = ObjC.classes.NSURLRequest["- initWithURL:"];
// Intercept the method
Interceptor.attach(URL.implementation, {
onEnter: function(args) {
// Get a handle on NSString
var NSString = ObjC.classes.NSString;
// Obtain a reference to the NSLog function, and use it to print the URL value
// args[2] refers to the first method argument (NSURL *url)
var NSLog = new NativeFunction(Module.findExportByName('Foundation', 'NSLog'), 'void', ['pointer', '...']);
// We should always initialize an autorelease pool before interacting with Objective-C APIs
var pool = ObjC.classes.NSAutoreleasePool.alloc().init();
try {
// Creates a JS binding given a NativePointer.
var myNSURL = new ObjC.Object(args[2]);
// Create an immutable ObjC string object from a JS string object.
var str_url = NSString.stringWithString_(myNSURL.toString());
// Call the iOS NSLog function to print the URL to the iOS device logs
NSLog(str_url);
// Use Frida's console.log to print the URL to your terminal
console.log(str_url);
} finally {
pool.release();
}
}
});
"""
process = frida.get_usb_device().attach("Safari")
script = process.create_script(frida_code)
script.load()
sys.stdin.read()
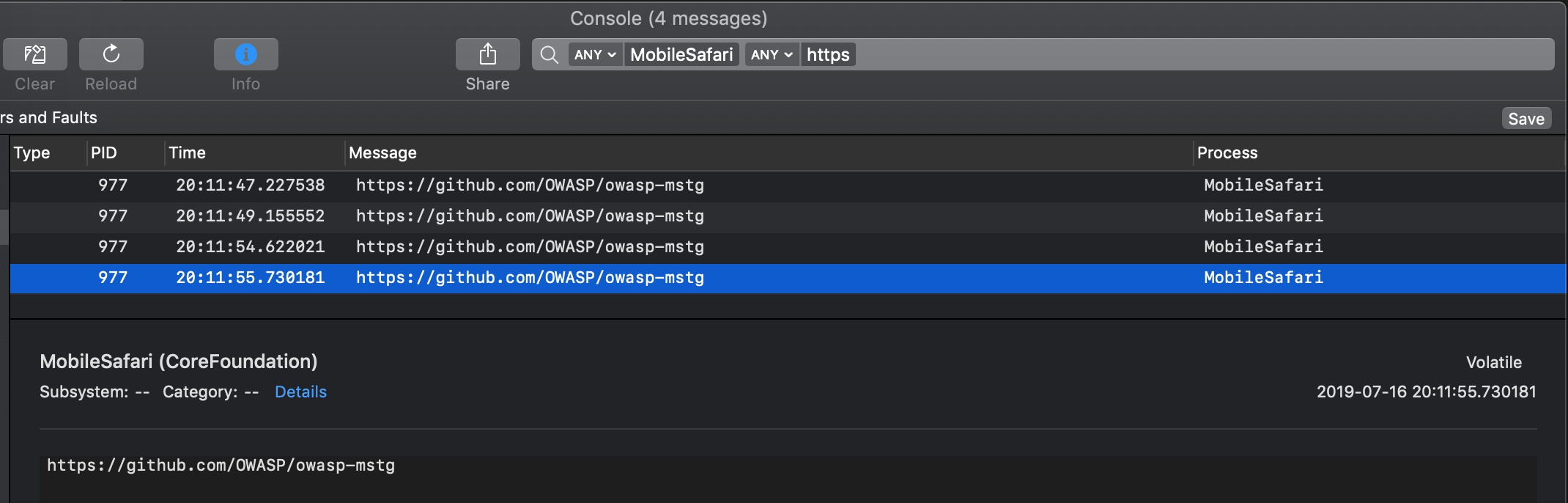
Start Safari on the iOS device. Run the Python script above on your connected host and open the device log (as explained in the section "Monitoring System Logs" in the chapter "iOS Basic Security Testing"). Try opening a new URL in Safari, e.g., https://github.com/OWASP/mastg. You should see Frida's output in the logs and in your terminal.
Of course, this example illustrates only one of the things you can do with Frida. To unlock the tool's full potential, you should learn to use its JavaScript API. The documentation section of the Frida website has a tutorial and examples for using Frida on iOS.
Tests¶
MASTG-TEST-0349: Runtime Use of Insecure Random APIs MASTG-TEST-0246: Runtime Use of Secure Screen Lock Detection APIs MASTG-TEST-0354: Runtime Use of Hook Detection Techniques MASTG-TEST-0271: Runtime Use Of APIs Detecting Biometric Enrollment Changes MASTG-TEST-0267: Runtime Use Of Event-Bound Biometric Authentication MASTG-TEST-0269: Runtime Use Of APIs Allowing Fallback to Non-Biometric Authentication MASTG-TEST-0336: Runtime Setting of Relaxed WebView File Origin Policies MASTG-TEST-0347: Runtime Use of APIs Hiding Sensitive Data in Text Input Fields MASTG-TEST-0301: Runtime Use of APIs for Storing Unencrypted Data in Private Storage MASTG-TEST-0296: Sensitive Data Exposure Through Insecure Logging MASTG-TEST-0314: Runtime Monitoring of Text Fields Eligible for Keyboard Caching MASTG-TEST-0298: Runtime Monitoring of Files Eligible for Backup